A teleprinter (teletypewriter, teletype or TTY) is an electromechanical device that can be used to send and receive typed messages through various communications channels, in both point-to-point and point-to-multipoint configurations.
Initially they were used in telegraphy, which developed in the late 1830s and 1840s as the first use of electrical engineering, though teleprinters were not used for telegraphy until 1887 at the earliest.
The machines were adapted to provide a user interface to early mainframe computers and minicomputers, sending typed data to the computer and printing the response. Some models could also be used to create punched tape for data storage (either from typed input or from data received from a remote source) and to read back such tape for local printing or transmission.
One such (deprecated in these days (2022)) computer-based teletype device, was the portable Minitel.
The Minitel was a videotex online service accessible through telephone lines, and was the world's most successful online service prior to the World Wide Web. It was invented in Cesson-Sévigné, near Rennes in Brittany, France.
The service was rolled out experimentally on 15 July 1980 in Saint-Malo, France, and from autumn 1980 in other areas, and introduced commercially throughout France in 1982 by the PTT (Postes, Télégraphes et Téléphones; divided since 1991 between France Télécom and La Poste).
From its early days, users could make online purchases, make train reservations, check stock prices, search the telephone directory, have a mail box, and chat in a similar way to what is now made possible by the World Wide Web (Internet).
In February 2009, France Télécom indicated the Minitel network still had 10 million monthly connections. France Télécom retired the service on 30 June 2012.
The service was purely PSTN-based (aka public switched telephone network / "plain old telephone system") and required a subscription land-line.
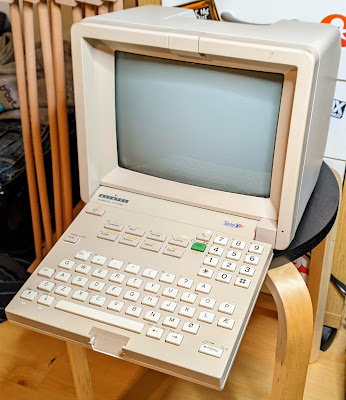
Recently I came over a Norwegian model on a Norwegian auction-site (finn.no), which would be the ideal complement to my next hobby-project: a PDP11/70 Unix mini-replica minicomputer. So I bought it.
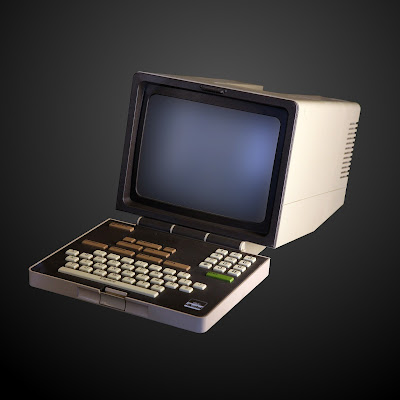
This is the Alcatel Terminus 258. A Minitel2-clone made for the Norwegian telecom authority at the time (Televerket, branded on the keyboard-latch in the image above).
The specimen I have is the Unitel-version, meaning; it is not catered for the Minitel-service, but as a control terminal using either a PSTN (Public Switched Telephone Network) or a serial (DIN connector) uplink.